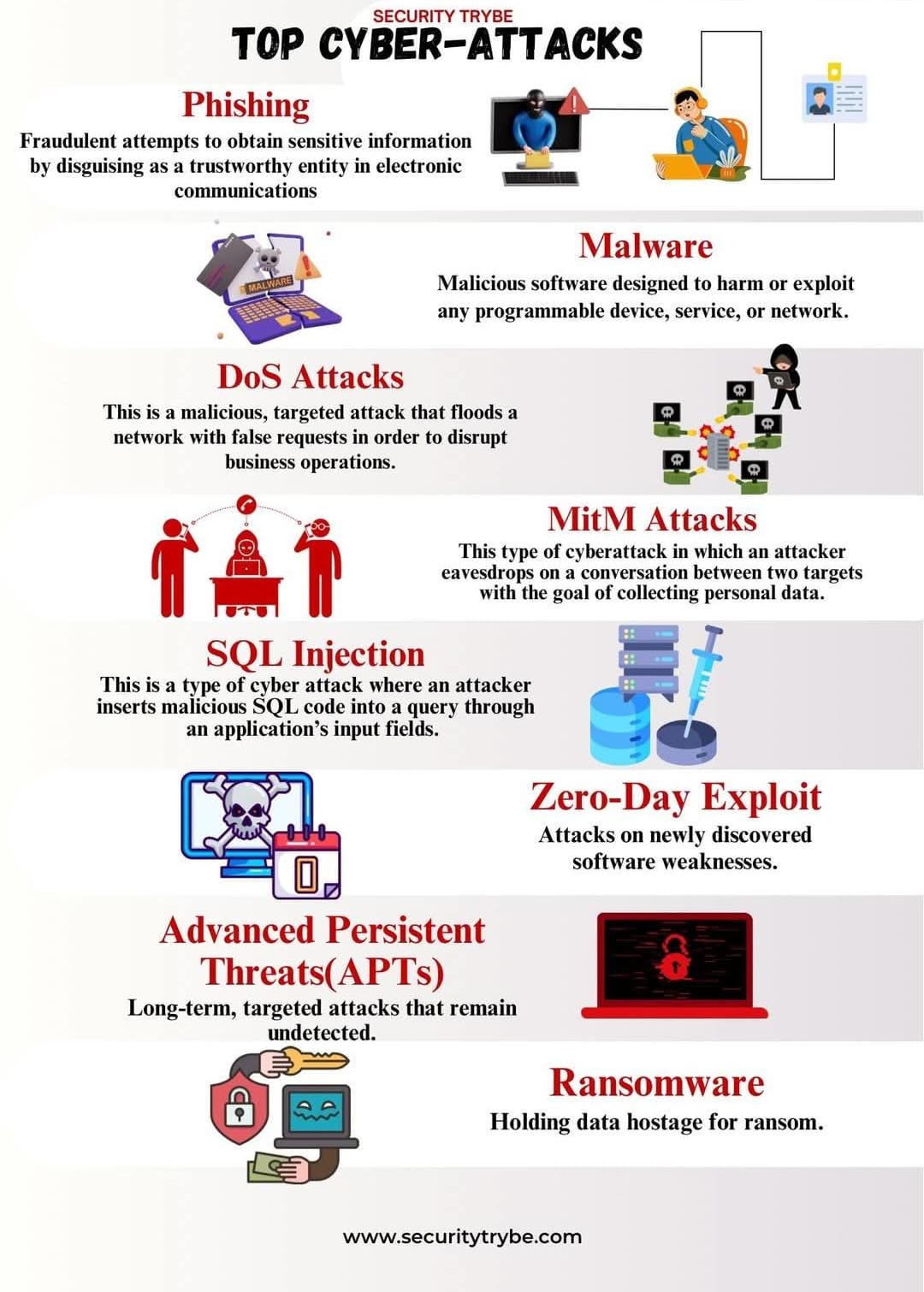
Here are eight of the most frequently used types of cyberattacks, from phishing and malware to SQL injection, zero-day exploits, APTs, and ransomware. These are summarized to help you stay vigilant at all times.
- Phishing: A fraudulent attempt to impersonate a trusted party to steal sensitive data.
- Malware/Ransomware: A malicious program that steals data or blocks access, demanding a ransom to restore access.
- DoS/DDoS: An attack that floods a system with fake traffic, making the service unavailable.
- MitM (Man-in-the-Middle): Undetected interception of communications between two parties, often used to steal data.
- SQL Injection: Inserting malicious code into application input to compromise or damage a database.
- Zero-Day Exploit: Exploiting a security vulnerability in software that is unknown to the vendor and has not yet been patched.
- APT (Advanced Persistent Threat): A long-term, targeted attack that penetrates undetected and systematically steals information.